Welcome to ChatCrypt
An end-to-end encrypted group chat that doesn't store anything in the cloud. No databases, no accounts, no chat logs.
Aimed for anyone who wants to be sure that their conversations are kept private and prefers more security over fancy features. It does not try to replace popular messaging applications, but instead to provide an alternate, secure channel for confidential discussions.
CHATCRYPT HAS NOTHING TO DO WITH CRYPTOCURRENCIES. A lot of messages have been received in the past couple of weeks saying that you cannot access your crypto wallet and such. Look elsewhere - this is only a chat. Do not ever give out your sensitive information, like passwords, to anyone.
Introduction
Our goal was to create an anonymous chat platform which can be used safely over inspected infrastructures so that conversations cannot be recovered even if the server has been seized or one of the participants has been questioned.
We have created a unique solution which does not require any sort of data storage and makes sure that messages cannot be decrypted even with the complete knowledge of the server contents, network traffic, and provided secret passwords.
Highlights
Triple encryption - Two additional security layers protect messages, on top of the standard TLS protocol.
Outstanding privacy - Conversations can happen without providing any personal detail or account.
Real-time messaging - Each piece of data is exchanged immediately between the parties; nothing is queued or stored, even for a single second.
How it works
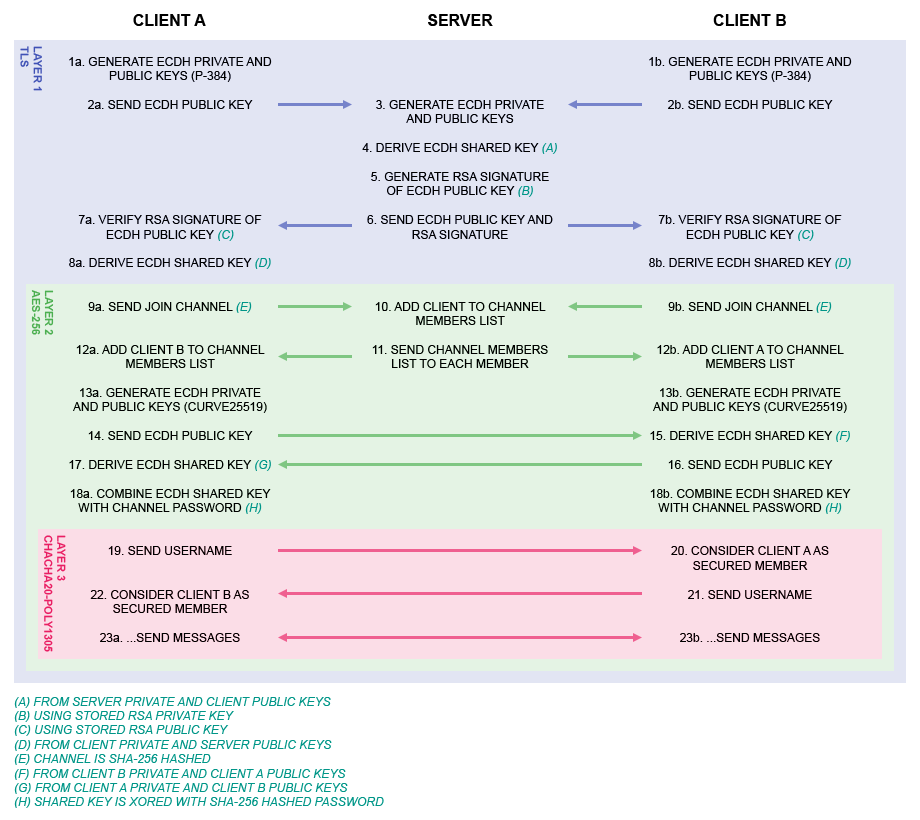
The client application establishes a WebSocket (over TLS) connection with the chat server. Then they create an additional encrypted layer, using ECDH for key exchange and AES-256 for ciphering. During key exchange, messages from the server are RSA-signed and verified by the client to make sure it is not connecting to a forged destination. This second layer also prevents transparent proxies (with their own CA certificates installed on the client) from inspecting their communication.
Once the server connection is secured, it joins the given channel and starts building up end-to-end encrypted layers with each individual member (using ECDH for key exchange and ChaCha20-Poly1305 for ciphering). Shared ECDH keys are combined with the provided channel passwords, which results in unique and one-time encryption keys between the parties. These keys cannot be reconstructed even with the knowledge of the second layers decrypted network traffic and the secret passwords. Additionally, this method ensures that members entering the same channel with a different password cannot communicate with each other.
It is worth mentioning that the channel password never leaves the client, the username is only transmitted over the third layer among the members, and the channel name is received by the server in an SHA-256 hashed form through the second layer.
Source code
We may provide the source code of the server and client application if given a well-founded request (e.g. educational use, security audit).
Privacy policy
We are committed to protecting and respecting your privacy. This privacy policy describes and governs our information collection, use, and sharing practices. Before you submit/upload any information or file to our websites, please carefully review this policy.
Data controller
For the purpose of data protection laws applicable to you in the location from which you provide your information, we are the "data controller" of the information you provide to our websites. There may be other controllers as well (e.g.: advertisers), and we encourage you to consult their privacy policies to learn more about their privacy practices.
Our primary data controller's contact:
Zoltan Hajdu
Email: contact@chatcrypt.com
Mobile: +36-30-608-85-50
Data storage and usage purposes
Please note that this privacy policy applies only to information collected through our websites and not to any information you may provide to any third-party sites to which we may link.
We make use of web server log files. The information inside these log files includes IP address, date/time stamp, referring/exit page, and type of browser. We use this information solely to administer our websites.
We use third-party ad server services Google Adsense, PubMax Ads and Publift Fuse; web analytics service Google Analytics, and a consent management platform from InMobi.
We and our third-party service providers (detailed above) may also store and collect data related to your use of our websites for the following purposes. Please note that by rejecting any or all of them, you may not have access to certain features or offerings of our websites.
Use precise geolocation data. Your precise geolocation data can be used in support of one or more purposes. "Precise" means your location can be accurate to within several meters.
Actively scan device characteristics for identification. Your device can be identified based on a scan of your device's unique combination of characteristics.
Select basic ads. Ads can be shown to you based on the content you're viewing, the app you're using, your approximate location, or your device type.
Create a personalised ads profile. A profile can be built about you and your interests to show you personalised ads that are relevant to you.
Select personalised ads. Personalised ads can be shown to you based on a profile about you.
Create a personalised content profile. A profile can be built about you and your interests to show you personalised content that is relevant to you.
Select personalised content. Personalised content can be shown to you based on a profile about you.
Measure ad performance. The performance and effectiveness of ads that you see or interact with can be measured.
Measure content performance. The performance and effectiveness of content that you see or interact with can be measured.
Apply market research to generate audience insights. Market research can be used to learn more about the audiences who visit particular sites/apps and view ads.
Develop and improve products. Your data can be used to improve existing systems or software and to develop new products.
Store and/or access information on a device. Cookies, device identifiers, or other information can be stored or accessed on your device for the above purposes presented to you.
Data retention
Our web server log files are deleted after 90 days.
Our Google Analytics tracking code is configured to store data that is associated with cookies, user identifiers, or advertising identifiers for up to 12 months.
If you require more information or have any questions about our privacy policy, please feel free to contact us.
Terms of use
Be advised that ChatCrypt is a hobby project and provided entirely "as is," without warranty of any kind.
However, there have been no complaints so far.
Contact us
Email: contact@chatcrypt.com
Please feel free to contact us with any questions or suggestions.